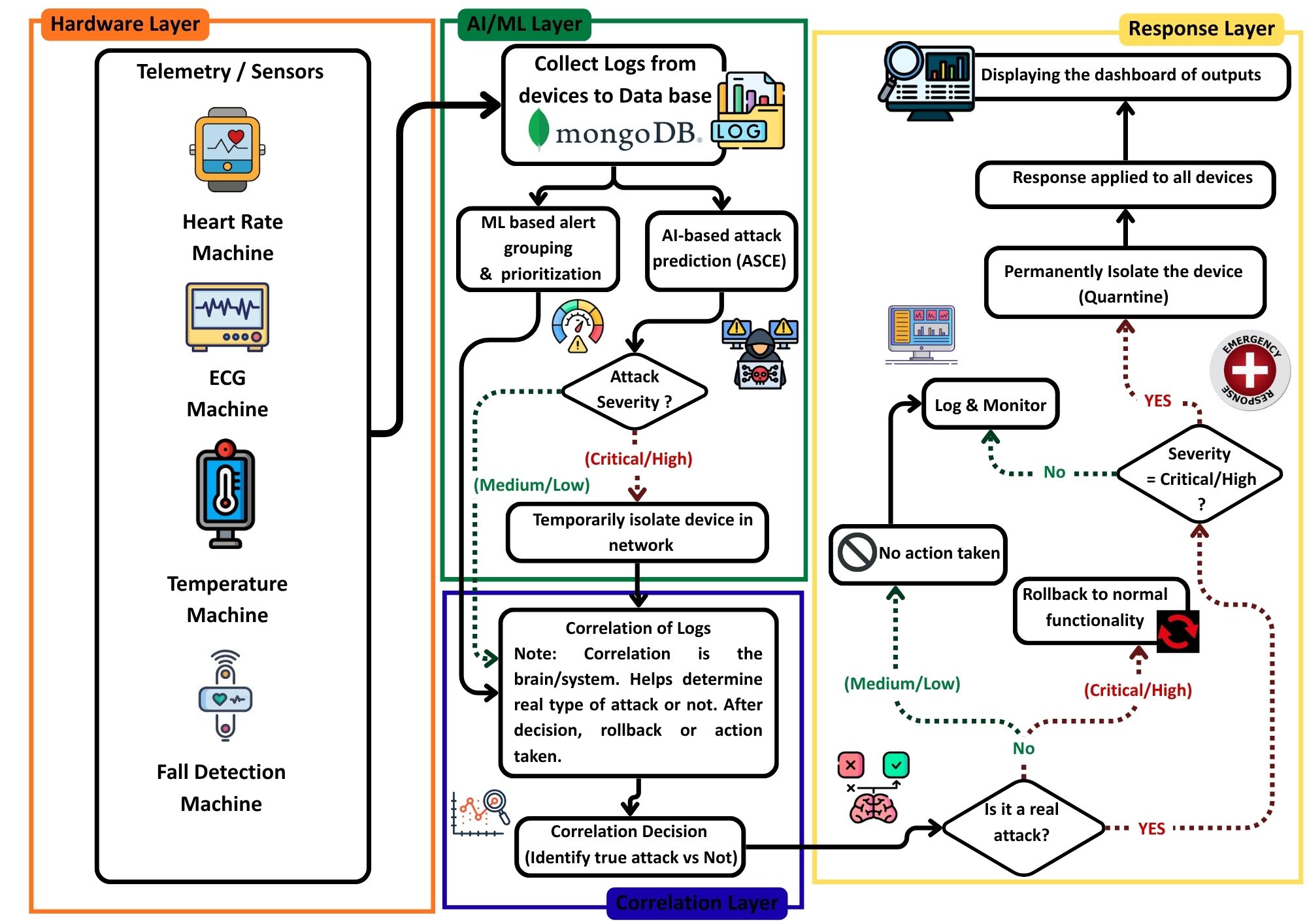
PROTOCOL: AICE-CORRELATION
Autonomous Incident Correlation
An intelligent engine that fuses heterogeneous alerts from network and host layers to reduce false positives by 40%.
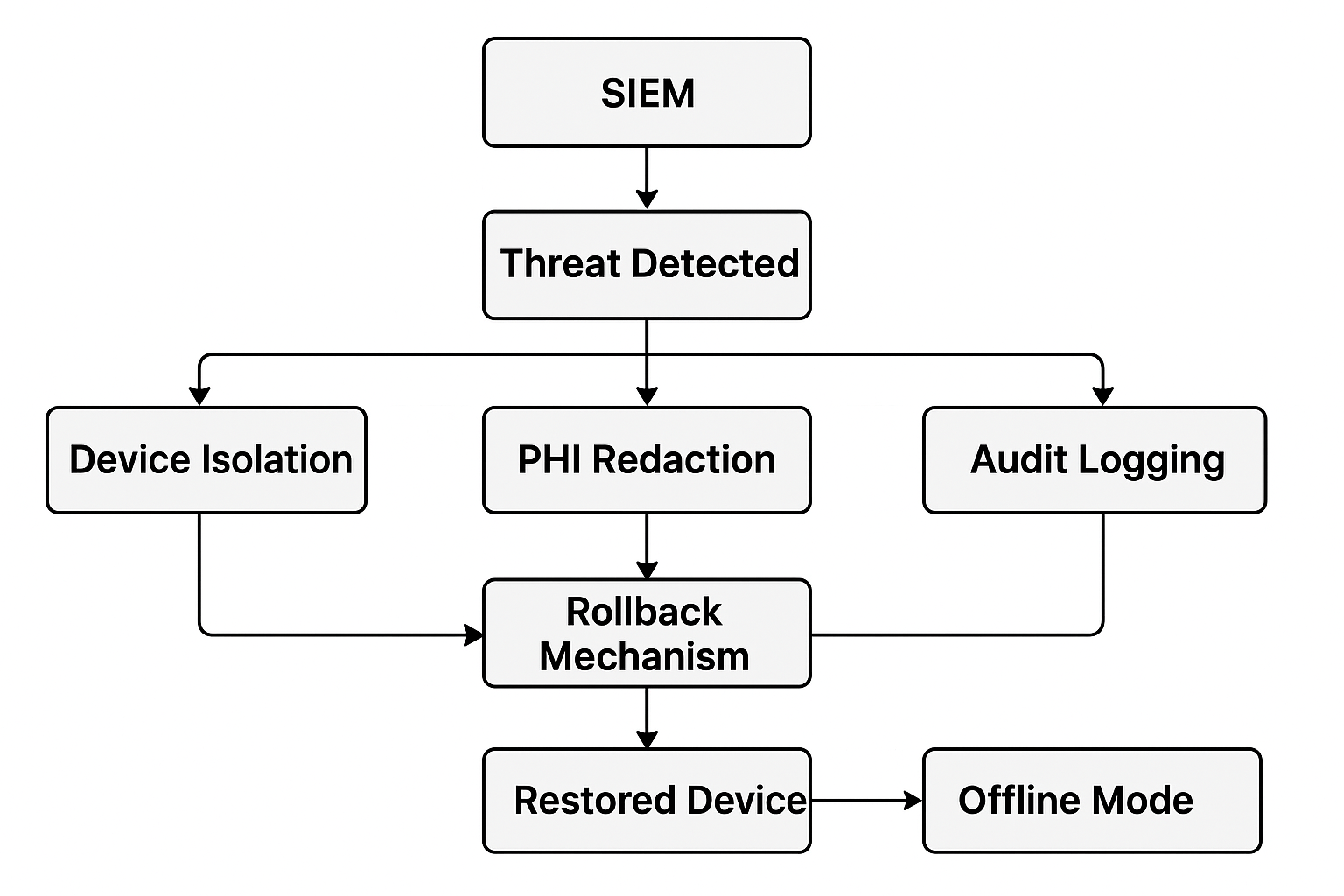
PROTOCOL: PRIVACY-MASK
Dynamic PHI Redaction
Ensuring HIPAA compliance through AI-driven masking of sensitive patient health information in real-time telemetry.
PROTOCOL: ZERO-TRUST-ISO
Proactive Threat Isolation
Autonomous containment protocol that predicts and isolates infected sensor nodes in <30s to prevent lateral movement.
PROTOCOL: SELF-HEAL-V1
Self-Healing Firmware Rollback
Integrated hardware mechanism to automatically restore compromised sensor firmware to a verified "last-known-good" state.
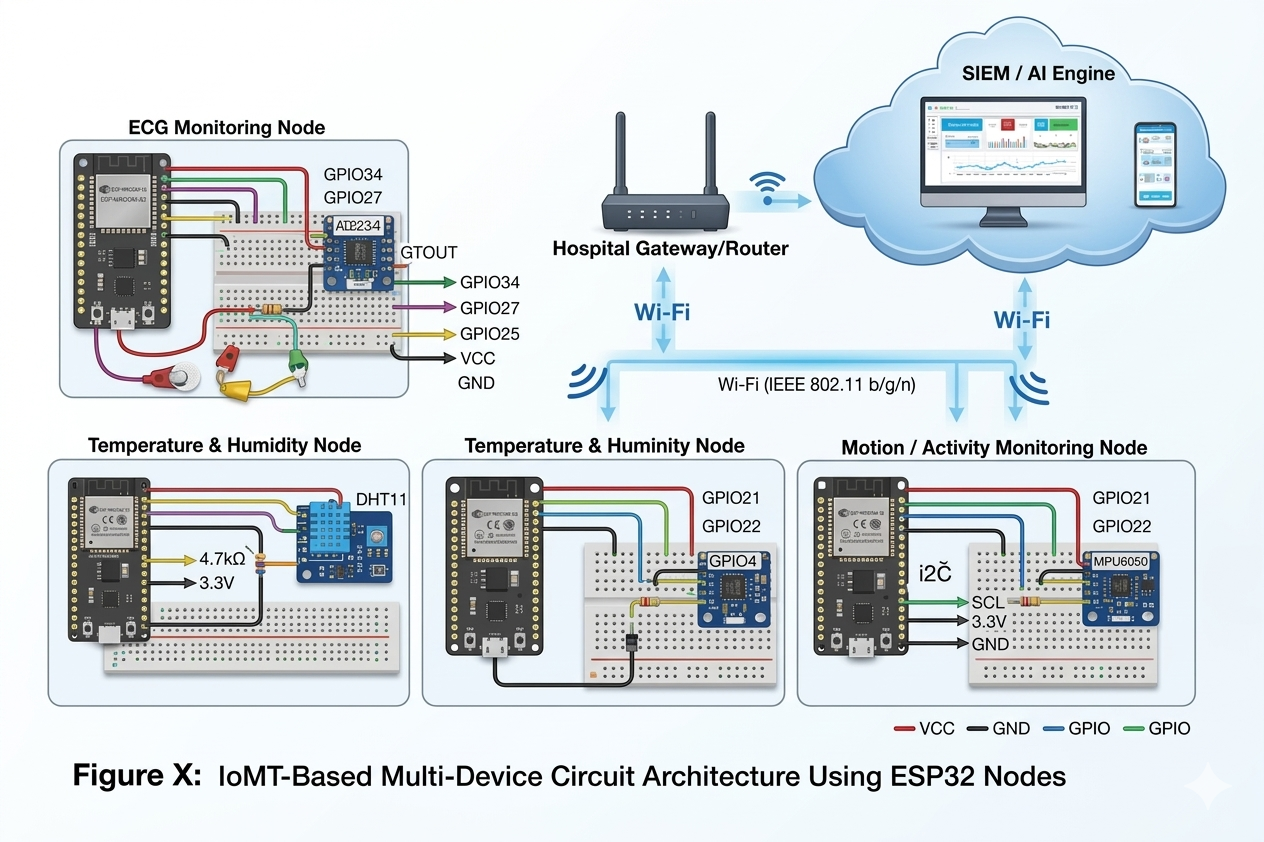
PROTOCOL: LIGHT-CLASSIFY
Resource-Optimized AI
Specially pruned ML models designed to run on resource-constrained ESP32 nodes without compromising detection accuracy.
PROTOCOL: QUAD-SYNC
Full-Stack Layer Synergy
Seamless bidirectional communication between Hardware, AI, Correlation, and Response layers for unified defense.